Featured
Table of Contents
- – Ipsec Explained: What It Is And How It Works
- – What Is Ipsec Protocol? How Ipsec Vpns Work
- – What Is Ipsec?
- – Understanding Ipsec Vpn Tunnels
- – What Is Ipsec?
- – What Is Ipsec?
- – Ipsec Explained: What It Is And How It Works
- – What Is Ipsec? How Does Ipsec Work?
- – What Is Ipsec Vpn - Ssl Vs Ipsec Protocol In...
- – Ssl Vpns Vs. Ipsec Vpns: Vpn Protocol Differ...
Ipsec Explained: What It Is And How It Works
Depending on the level of security needed, VPN companies can implement both or choose one over the other. SSL VPNs rely on the procedure.
Thus, the security and applications of IPSec VPN and SSL VPN vary. With IPSec VPN, your traffic is protected as it moves to and from private networks and hosts; in a nutshell, you can secure your whole network.
What Is Ipsec Protocol? How Ipsec Vpns Work

We have all heard of SSL. SSL is what enables things like e-commerce to thrive. SSL lets us interact with websites safely, but what do we do if we require to link to another network independently rather of a site? That's when you use IPSec. A lot of new IT techs and system admins do not fully comprehend IPSec.
IPSec is a method of secure, encrypted communications in between a client and a network. That interaction is sent out through public networks such as the web.
What Is Ipsec?
That implies that IPSec can possibly be more safe than other approaches of secure communication. IPSec connections are still made between the customer and host through other networks.
Both the client and the host requirement to understand the private encryption secret prior to connections can be developed. That last bit is necessary. That's since the whole package of information is encrypted during interactions. That consists of the packet header, too. You might believe that all packages require legible headers to get to their destination appropriately, and you would be right.
Understanding Ipsec Vpn Tunnels
ESP includes brand-new header details and trailers (similar to headers but at the end of a package) for transportation while the actual header remains encrypted. Each package is validated too. The IPSec host will verify that each package of information got was sent out by the entity that the host thinks sent it.
IPSec is used to develop a protected approach of communication in between a client and a host. The host is normally a private network, too. We understand how IPsec works, but what is IPSec used for?
What Is Ipsec?

Today, however, they can interact over the open internet utilizing an IPsec connection. In many ways, an IPsec connection and a TLS or SSL connection are similar. Both supply a method for secure, encrypted communications. Both can utilize public networks for interaction. Etc. In lots of other methods, though, IPsec and TLS or SSL connections are extremely various, too.
Thus, IPsec connections begin at the basic connection level of the OSI design. On the other hand, TLS and SSL connections begin higher up the stack. Second, TLS and SSL connections depend on the application layer (HTTP) and layer 4 (TCP) to work. That implies they are also susceptible to exploits in those layers, whereas IPsec might not be.
What Is Ipsec?
Since TLS and SSL connections utilize TCP, those safe connection types need to be negotiated. IPSec is various.
The method used for essential exchanges in IPsec is called IKEv1 or IKEv2. Because IPsec connections are encrypted instantly, the whole header of the IP packet can be secured, too.
Ipsec Explained: What It Is And How It Works
That implies the MSS and MTU sizes for each package will change. Network admins require to make sure to make allowances for those size distinctions in their network. We covered a lot of information in this short article! So, let's evaluate it quickly. IPSec is an approach of protected, encrypted interaction between a customer and a host.
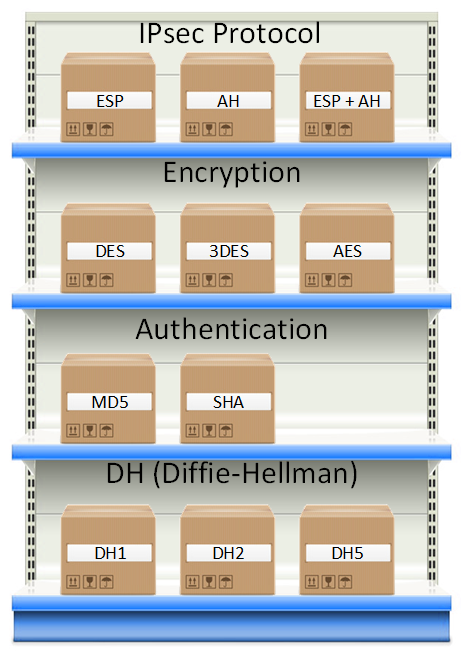
The host is generally a private network. IPsec itself is not a protocol but rather a handful of protocols used together.
What Is Ipsec? How Does Ipsec Work?
Virtual personal network (VPN) is a technology for establishing a private network on a public network. It is a rational network over a public network such as the Internet, enabling user information to be transmitted through a sensible link. This is different from a standard personal network, where user information is transferred through an end-to-end physical link.
In this phase, the interacting parties utilize the Internet Secret Exchange (IKE) protocol to establish IKE SAs for identity authentication and key information exchange, and after that establish IPsec SAs for secure information transmission based upon the IKE SAs. Data transmission. After IPsec SAs are developed in between the communicating parties, they can transfer information over an IPsec tunnel.
What Is Ipsec Vpn - Ssl Vs Ipsec Protocol In 2023
If the ICVs obtained at both ends are the same, the packet is not tampered with throughout transmission, and the receiver decrypts the package. If the ICVs are different, the receiver discards the packet. IPsec encryption and authentication process Tunnel teardown. In many cases, session aging (session disconnection) between two interaction celebrations indicates that data exchange in between the 2 communication celebrations is complete.
That is, AH guarantees that the source of IP packets is trusted and the data is not tampered with. AH, nevertheless, does not provide the encryption function. An AH header is appended to the basic IP header in each information package. AH checks the stability of the whole IP packet.
Ssl Vpns Vs. Ipsec Vpns: Vpn Protocol Differences ...
An ESP header is added to the standard IP header in each data packet, and the ESP Trailer and ESP Auth information fields are appended to each information package. ESP in transport mode does not inspect the stability of IP headers. ESP can not make sure that IP headers are not tampered with.
The following compares IPsec VPN and SSL VPN: Working layers of the OSI recommendation model, OSI defines a seven-layer framework for network interconnection: physical layer, information connect layer, network layer, transport layer, session layer, discussion layer, and application layer. IPsec operates at the network layer and directly runs over the Web Procedure (IP).
Table of Contents
- – Ipsec Explained: What It Is And How It Works
- – What Is Ipsec Protocol? How Ipsec Vpns Work
- – What Is Ipsec?
- – Understanding Ipsec Vpn Tunnels
- – What Is Ipsec?
- – What Is Ipsec?
- – Ipsec Explained: What It Is And How It Works
- – What Is Ipsec? How Does Ipsec Work?
- – What Is Ipsec Vpn - Ssl Vs Ipsec Protocol In...
- – Ssl Vpns Vs. Ipsec Vpns: Vpn Protocol Differ...
Latest Posts
The Best Vpn For Business In 2023: Top 8 Corporate ...
Best Mobile Vpn
Best Virtual Private Network (Vpn) Software 2023
More
Latest Posts
The Best Vpn For Business In 2023: Top 8 Corporate ...
Best Mobile Vpn
Best Virtual Private Network (Vpn) Software 2023