Featured
Table of Contents
- – Ipsec (Internet Protocol Security) Vpn
- – 1. Define Ipsec? 2. What Ipsec Used For? 3. Wh...
- – Using Sauce Ipsec Proxy
- – What You Need To Know About Internet Protocol...
- – Ssl Vpns Vs. Ipsec Vpns: Vpn Protocol Differe...
- – About Virtual Private Network (Ipsec) - Tech...
- – What Is An Ipsec Vpn?
- – Ipsec Overview
- – What Is Ipsec And How It Works
- – Ipsec Overview
Ipsec (Internet Protocol Security) Vpn
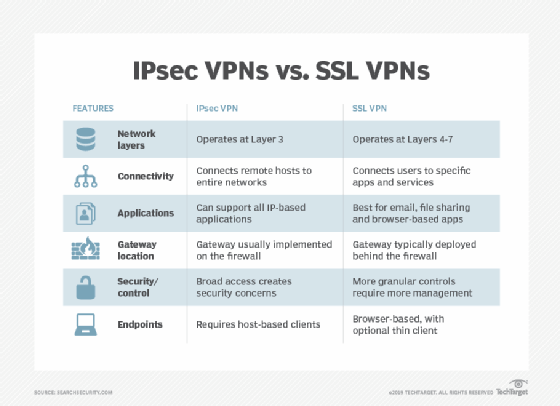
Depending on the level of security required, VPN providers can carry out both or select one over the other. SSL VPNs rely on the protocol.
Therefore, the security and applications of IPSec VPN and SSL VPN vary. With IPSec VPN, your traffic is secure as it moves to and from private networks and hosts; in a nutshell, you can protect your entire network.
1. Define Ipsec? 2. What Ipsec Used For? 3. What Are The ...
That's when you utilize IPSec. A lot of new IT techs and system admins do not totally comprehend IPSec.
IPSec is a technique of secure, encrypted interactions in between a customer and a network. That interaction is sent through public networks such as the internet.
Using Sauce Ipsec Proxy
That means that IPSec can potentially be more protected than other approaches of safe and secure communication. IPSec connections are still made between the customer and host through other networks.
Both the customer and the host requirement to know the private encryption secret before connections can be established. That last bit is necessary. That's because the whole packet of data is secured throughout communications. That includes the package header, too. You may believe that all packets require readable headers to get to their location correctly, and you would be.
What You Need To Know About Internet Protocol Security ...
ESP adds new header information and trailers (similar to headers however at the end of a package) for transportation while the real header remains encrypted. Each package is authenticated too. The IPSec host will verify that each package of information received was sent by the entity that the host thinks sent it.
IPSec is used to create a safe and secure approach of communication between a customer and a host. That customer could be something like a laptop computer. That client could also be a personal network. The host is typically a private network, too. We know how IPsec works, however what is IPSec utilized for? What does that paragraph above even imply? IPSec is typically used for VPNs.
Ssl Vpns Vs. Ipsec Vpns: Vpn Protocol Differences ...

Today, however, they can interact over the open internet using an IPsec connection. In lots of methods, an IPsec connection and a TLS or SSL connection are similar. In lots of other ways, though, IPsec and TLS or SSL connections are incredibly different, too.
Hence, IPsec connections begin at the fundamental connection level of the OSI design. That suggests they are also vulnerable to exploits in those layers, whereas IPsec may not be.
About Virtual Private Network (Ipsec) - Techdocs
Since TLS and SSL connections utilize TCP, those secure connection types require to be negotiated initially. Once worked out, the customer and host will settle on an encryption key, too. IPSec is different. Interaction is encrypted immediately. The secret key utilized for file encryption requires to be shared between the customer and host independently before any communications can be attempted.
The technique utilized for crucial exchanges in IPsec is called IKEv1 or IKEv2. Because IPsec connections are secured instantly, the whole header of the IP packet can be secured, too.
What Is An Ipsec Vpn?
That means the MSS and MTU sizes for each packet will change. Network admins require to make sure to consider those size distinctions in their network. We covered a great deal of details in this article! So, let's evaluate it rapidly. IPSec is an approach of safe and secure, encrypted interaction in between a client and a host.
The host is normally a private network. IPsec itself is not a protocol but rather a handful of protocols utilized together. The protocols that IPsec utilizes start at Layer 3 of the OSI design, making IPsec possibly more safe than things like TLS or SSL.IPsec is generally used for VPNs.
Ipsec Overview
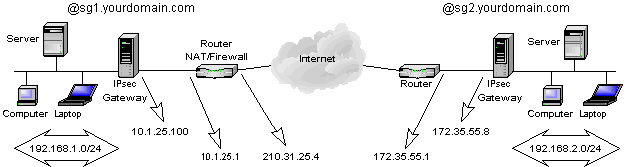
Virtual private network (VPN) is a technology for developing a private network on a public network. It is a logical network over a public network such as the Internet, enabling user data to be transferred through a logical link. This is various from a traditional personal network, where user information is sent through an end-to-end physical link.
In this phase, the communicating parties use the Internet Secret Exchange (IKE) procedure to develop IKE SAs for identity authentication and essential info exchange, and after that establish IPsec SAs for protected information transmission based upon the IKE SAs. Data transmission. After IPsec SAs are established in between the communicating parties, they can transfer information over an IPsec tunnel.
What Is Ipsec And How It Works
If the ICVs gotten at both ends are the exact same, the package is not tampered with during transmission, and the receiver decrypts the packet. IPsec file encryption and authentication process Tunnel teardown.
That is, AH guarantees that the source of IP packets is trusted and the data is not tampered with. AH, however, does not offer the encryption function. An AH header is appended to the standard IP header in each information package. AH checks the integrity of the whole IP package.
Ipsec Overview
An ESP header is added to the basic IP header in each data packet, and the ESP Trailer and ESP Auth information fields are appended to each information package. ESP in transportation mode does not inspect the integrity of IP headers. ESP can not guarantee that IP headers are not tampered with.
The following compares IPsec VPN and SSL VPN: Working layers of the OSI referral model, OSI specifies a seven-layer framework for network affiliation: physical layer, data connect layer, network layer, transport layer, session layer, discussion layer, and application layer. IPsec works at the network layer and directly runs over the Internet Protocol (IP).
Table of Contents
- – Ipsec (Internet Protocol Security) Vpn
- – 1. Define Ipsec? 2. What Ipsec Used For? 3. Wh...
- – Using Sauce Ipsec Proxy
- – What You Need To Know About Internet Protocol...
- – Ssl Vpns Vs. Ipsec Vpns: Vpn Protocol Differe...
- – About Virtual Private Network (Ipsec) - Tech...
- – What Is An Ipsec Vpn?
- – Ipsec Overview
- – What Is Ipsec And How It Works
- – Ipsec Overview
Latest Posts
The Best Vpn For Business In 2023: Top 8 Corporate ...
Best Mobile Vpn
Best Virtual Private Network (Vpn) Software 2023
More
Latest Posts
The Best Vpn For Business In 2023: Top 8 Corporate ...
Best Mobile Vpn
Best Virtual Private Network (Vpn) Software 2023