Featured
Table of Contents
- – Openvpn Vpn Protocol
- – Aws Vpn - Faqs - Amazon Web Services (Aws)
- – What Are Vpn Tunnels And How Do They Work
- – What Is Openvpn?
- – What Is Openvpn Protocol? - Nordlayer Learn
- – What Is Openvpn? [A Beginner-friendly Guide]
- – Openvpn Vpn Protocol
- – Comparing Openvpn Vs. L2tp/ipsec [Ultimate B...
- – Ipsec Vs Openvpn: Which One Should You Use?
- – What Does A Vpn App Do & How Does It Work?
- – What Is Openvpn - Is It Safe & How Does It W...
Openvpn Vpn Protocol
This guarantees you're always safeguarded online. A little con is that PIA is based in the US, part of the 5 Eyes Alliance. Governments within the alliance deserve to ask for user data from VPN business and can share it with other nations. However,. Long-term strategies are cost effective at $2.
Both are open-source VPN procedures, including to their transparency and overall security. To check which works best for you, pick a VPN that supports both. Supplies a high level of security through SSL/TLS file encryption and several authentication methods Utilizes advanced cryptography for secure connections Highly configurable Designed to be easy to use and deploy Suitable with lots of VPN providers and devices/operating systems Less setup choices, but this may alter as Wire, Guard gains appeal Relatively high overhead that can result in slowdowns Utilizes fever code, making it much faster Developed and commonly utilized Newer VPN procedure Has been around longer, and thus examined more, adding to its trustworthiness Smaller sized code base, simpler to investigate for security vulnerabilities Can utilize TCP port 433, that makes it better at bypassing firewall softwares and network restrictions Only runs UDP Open, VPN is an open-sourced VPN protocol that's proven safe to utilize.
Aws Vpn - Faqs - Amazon Web Services (Aws)
It has military-grade file encryption and privacy functions that will guarantee your digital security, plus it's presently offering 49% off.
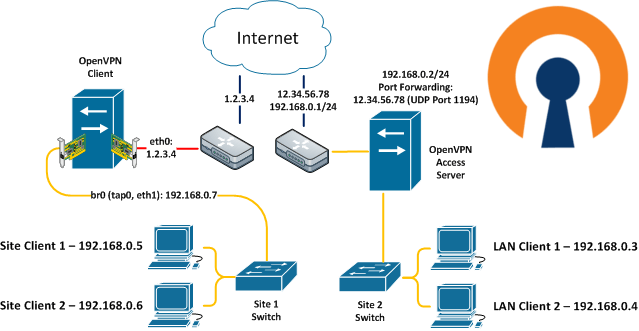
Open, VPN is an often used by VPN suppliers to secure users' point-to-point or site-to-site connections. The Open, VPN procedure is useful in client-server communications as it assists to develop highly secure connections between the VPN customer and the VPN server. It utilizes and sends online information utilizing either the User Datagram Protocol () or Transmission Control Procedure ().
What Are Vpn Tunnels And How Do They Work
It's what the majority of third-party VPN services offer for those who desire to set up Open, VPN on routers. Certificate Authority refers to the utilized to validate other certificates and keys when establishing connections in between VPN clients and a server.
Below are the actions on how to manually set up Open, VPN on your gadget. With a third-party VPN app that utilizes the Open, VPN tunneling protocol, the procedure will be automated.
What Is Openvpn?
If you are using a Windows PC, here are the steps to follow: Windows Key + E > This PC > System Characteristics to check whether your Windows OS is the 32-bit or 64-bit version. Go to to find the matching installer for your system type and download the proper one.
/ easyrsa clean-all The above steps are essential to set up the Open, VPN client properly. The next steps are crucial to create customer certificates and secrets.
What Is Openvpn Protocol? - Nordlayer Learn
Once you have set up the app on the devices, proceed to step 5. Now you simply need to import the certificates and secrets already produced in the steps above. To do this, just follow these actions: Copy the ca. crt, customer. crt and customer. crucial files from steps 2 and 3 above to the config directory site of each client gadget.
It is among the best protocols. If you choose a third-party VPN service, it's suggested that you opt for a service provider that uses it in order to enjoy a highly safe online experience without worry of hackers. We hope this guide addresses all questions about how Open, VPN works, how to set it up and when you must use it.
What Is Openvpn? [A Beginner-friendly Guide]
The first thing to understand about Open, VPN is that it is a VPN protocol. A protocol is a set of guidelines that. It determines how to encrypt and label information packages passing across VPN connections.
and was the first open-source VPN procedure. Since then, a worldwide community of developers has actually emerged. Open, VPN's open-source neighborhood checks bugs and improves the procedure, adding brand-new features and updating security components. Continuous examination means that the protocol is. Open, VPN is This suggests that it operates at the Transportation Layer (level 4) of the OSI model.
Openvpn Vpn Protocol
Open, VPN systems can serve a single workstation connecting to a company network or scale as much as enterprise-wide security systems. The VPN is created to cover as numerous gadgets as users need. Users download pre-configured clients, install them to their devices, and are all set to go. One of the biggest Open, VPN advantages is that users can install Open, VPN customers on Windows, Linux, and mac, OS.
Users will not require to trust that corporations secure information and avoid security mistakes. An around the world coding community tweaks Open, VPN to respond to the most current cybersecurity trends. The advantages noted above separate Open, VPN from the majority of other VPN procedures. No cybersecurity innovation is flawless. Open, VPN is no exception, and there are numerous possible weak points users require to understand about:.
Comparing Openvpn Vs. L2tp/ipsec [Ultimate Blog]
This is convenient, however business with bespoke security needs may discover other protocols more user-friendly. Open, VPN has actually become a streamlined service for desktop and laptop operating systems but is not as slick for mobile users. Android and i, OS implementations are not as innovative or easy to use, although they are enhancing all the time.
Once you have installed the app on the gadgets, move on to step 5. Now you just need to import the certificates and keys already created in the actions above. To do this, just follow these steps: Copy the ca.
Ipsec Vs Openvpn: Which One Should You Use?
It is among the most safe procedures. If you opt for a third-party VPN service, it's suggested that you choose a service provider that offers it in order to enjoy an extremely safe online experience without fear of hackers. We hope this guide answers all concerns about how Open, VPN works, how to set it up and when you ought to use it.

The very first thing to comprehend about Open, VPN is that it is a VPN procedure. A protocol is a set of guidelines that. It figures out how to encrypt and identify information packets passing across VPN connections.
What Does A Vpn App Do & How Does It Work?
Open, VPN's open-source community checks bugs and fine-tunes the procedure, including brand-new features and upgrading security components. Continuous scrutiny implies that the protocol is.
Open, VPN systems can serve a single workstation connecting to a company network or scale up to enterprise-wide security systems. One of the most significant Open, VPN benefits is that users can set up Open, VPN clients on Windows, Linux, and mac, OS.
What Is Openvpn - Is It Safe & How Does It Work?
A worldwide coding community tweaks Open, VPN to react to the newest cybersecurity trends. The advantages noted above different Open, VPN from a lot of other VPN protocols.
This is convenient, but companies with bespoke security needs may discover other procedures more user-friendly. Open, VPN has become a structured option for desktop and laptop computer operating systems but is not as slick for mobile users. Android and i, OS executions are not as sophisticated or easy to use, although they are improving all the time.
Table of Contents
- – Openvpn Vpn Protocol
- – Aws Vpn - Faqs - Amazon Web Services (Aws)
- – What Are Vpn Tunnels And How Do They Work
- – What Is Openvpn?
- – What Is Openvpn Protocol? - Nordlayer Learn
- – What Is Openvpn? [A Beginner-friendly Guide]
- – Openvpn Vpn Protocol
- – Comparing Openvpn Vs. L2tp/ipsec [Ultimate B...
- – Ipsec Vs Openvpn: Which One Should You Use?
- – What Does A Vpn App Do & How Does It Work?
- – What Is Openvpn - Is It Safe & How Does It W...
Latest Posts
The Best Vpn For Business In 2023: Top 8 Corporate ...
Best Mobile Vpn
Best Virtual Private Network (Vpn) Software 2023
More
Latest Posts
The Best Vpn For Business In 2023: Top 8 Corporate ...
Best Mobile Vpn
Best Virtual Private Network (Vpn) Software 2023